SECURITY & DATA PRIVACY
Ensure market research data privacy across qual research
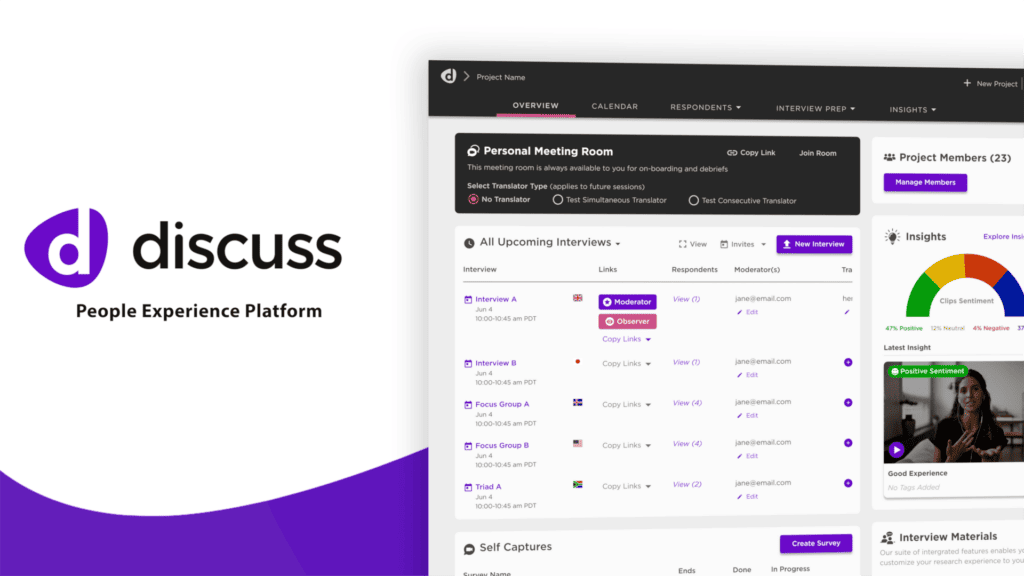
Keeping your data secure, private, and compliant is a top priority at Discuss. Our purpose-built qual platform not only helps you turn experiences into insights but also delivers peace of mind with a secure and privacy-centric approach.

Delivering industry-leading security best practices

ISO - 27001
Discuss has maintained the ISO 27001 certification since 2019. We continue to demonstrate our commitment to the highest level of trust and have shown our ability to comply with the most stringent international standards and reaffirm the importance of data and privacy protection.

GDPR
Our legal and information security teams have carefully analyzed the General Data Protection Regulation (GDPR) and have undertaken the necessary steps to ensure compliance. Discuss also offers processes to protect respondents' data from video blurring and audio distortion to personal data anonymization, and custom data retention rules.
CCPA
We are compliant with the California Consumer Privacy Act (CCPA), the most stringent data privacy law in the United States. Discuss does not sell your personal information or your end users’ personal information, and therefore do not offer an opt-out to the sale of personal information.

COPPA
Discuss is compliant with the Children's Online Privacy Protection Act of 1998, which prohibits unfair or deceptive acts with the collection, use, and/or disclosure of personal information from and about children on the Internet.
Key Capabilities
Take control of your market research data privacy
Access control
Users are in control of who has access to their projects and project materials. We support team-level and project-level access with role-based access controlled by the project owner. Project owners also manage project privacy, allowing them to share insights with their larger organization or keep findings private to a core team.
Anonymization
Data retention
Single sign on
Privacy controls
Featured Testimonial


Platform security and management
Data hosting and encryption
To ensure the integrity and confidentiality, all data is encrypted in transit and at rest using HTTPS. Our application servers and data is hosted on Amazon Web Services and stored in Viginia, USA.
Proactive monitoring and alerting
Our meeting room is designed with privacy in mind. Role-based permissions, authentication requirements, a waiting room, and moderator controls prevent unauthorized access and inappropriate activity within the meeting room.
Data breach management
We have a protocol in place for how to keep your data safe and secure if something goes wrong.
Reliability and backup
We use AWS automated backups and manual snapshots to prevent data loss before significant infrastructure change.
Disaster recovery
Our recovery plans identify the resources and specify actions required to help minimize losses in the event of service disruption.
Auditing
Annually, Discuss conducts an independent third-party review of its security policies, standards, operations, and procedures related to the services provided to customers.
Featured resources
Discover how leading global brands are using Discuss to unlock in-depth qualitative insights.